Phishing Mitigation: Techniques and Strategies

What Is a Spear Phishing Attack? Definition, Process, and Prevention Best Practices - Spiceworks
What does the future of phishing attacks look like?
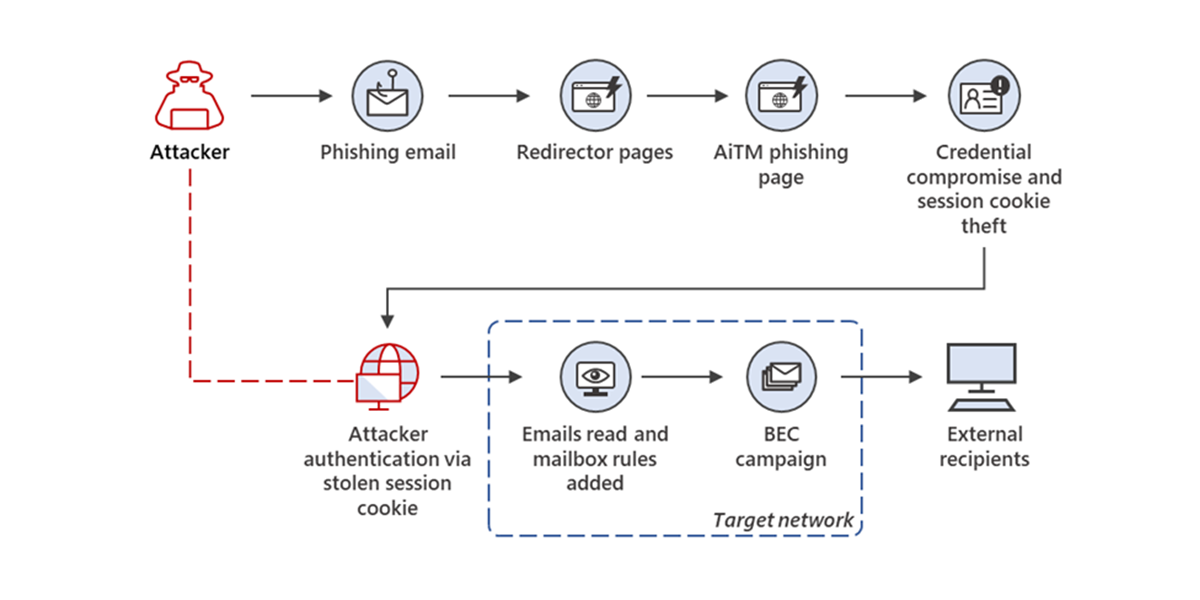
From cookie theft to BEC: Attackers use AiTM phishing sites as entry point to further financial fraud
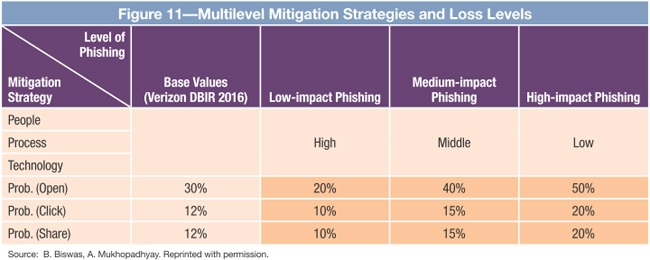
Phishing Detection and Loss Computation Hybrid Model: A Machine-learning Approach

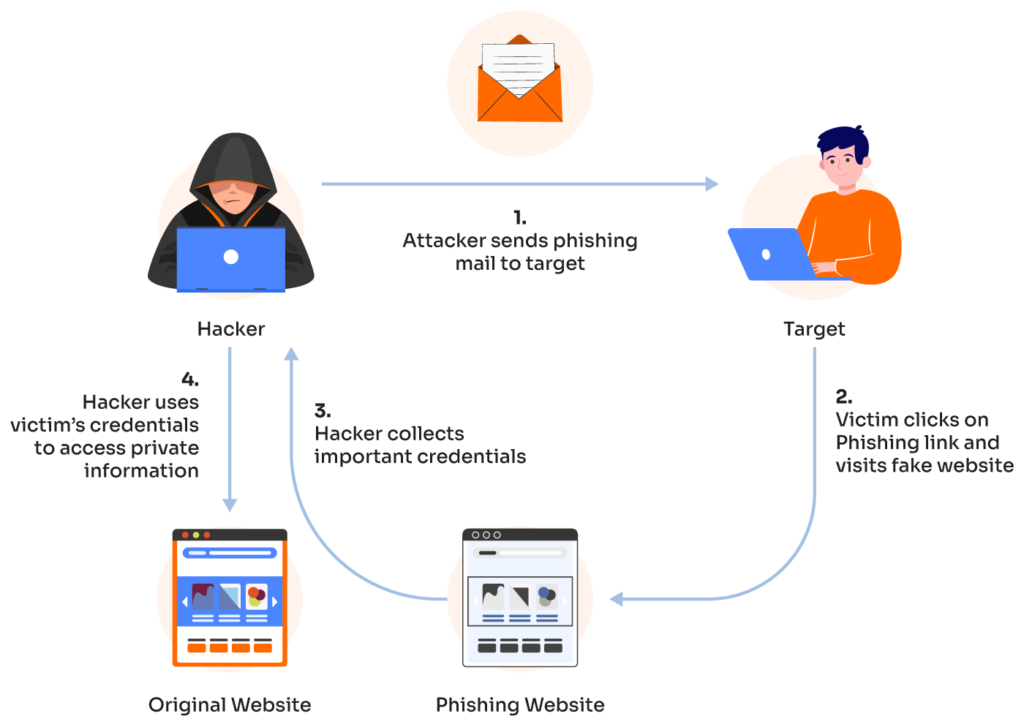
Phishing Attack Types and Mitigation: A Survey
Complete Guide to Phishing: Techniques & Mitigations - Valimail

6 Common Phishing Attacks and How to Protect Against Them

Phishing 2024: How to Protect Your Business from New Hacker Tactics - TrustNet

Pynesec Technologies on LinkedIn: #pynesectechnologies #cybersecurity #startup #hacking #vulnerability #xml…
Phishing Mitigation Strategies: 5 Effective Ways - PhishGrid

The Perils of Phishing Attacks: A Case Study on DocuSign — Protos Labs Singapore